Built with AI Tooling
Shipped Products
Production software directed with Claude Code and Gemini CLI, from architecture to deployment.
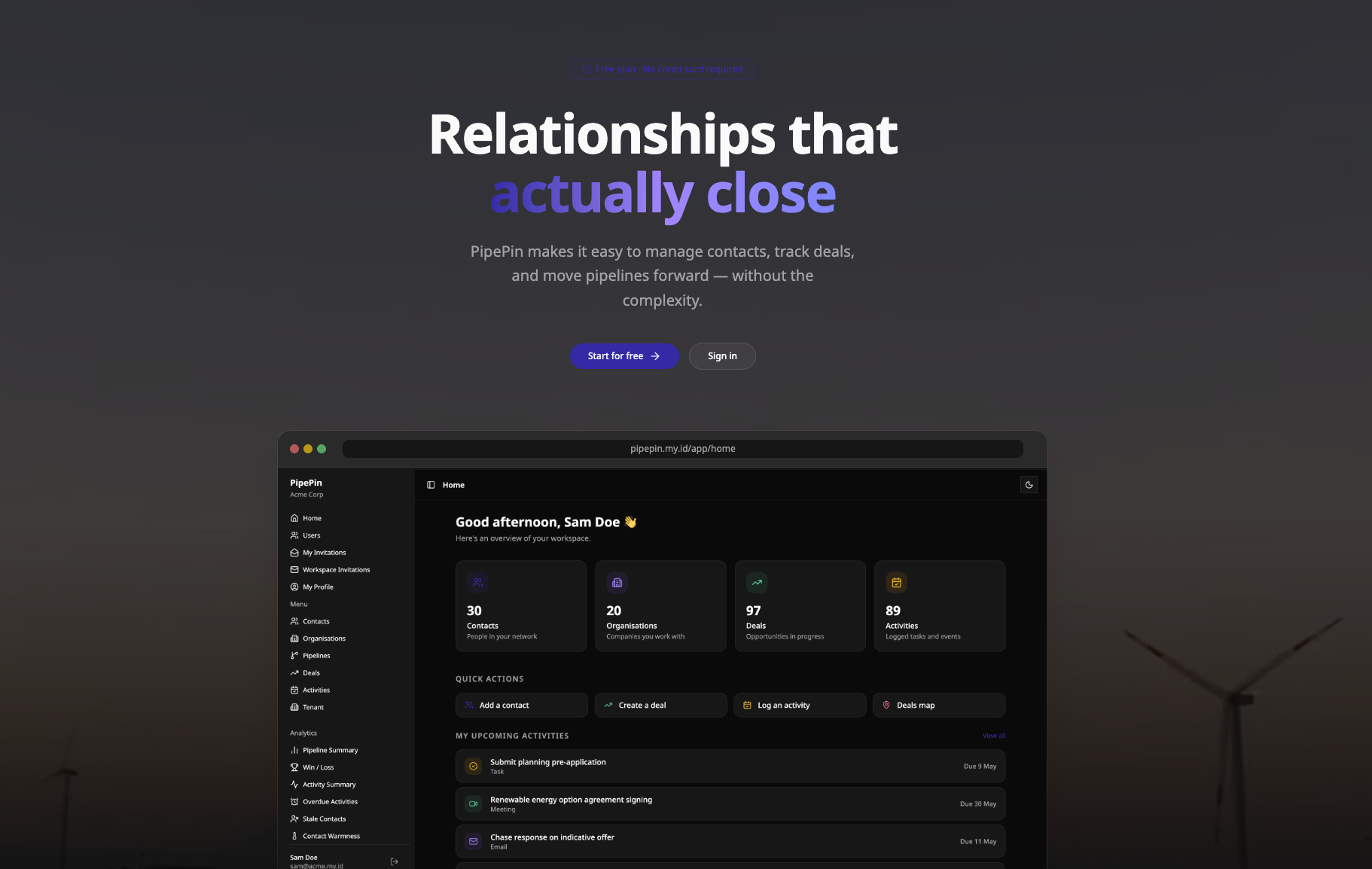
CRM · PropTech · Renewable Energy
pipepin.my.id
A map-based CRM built for renewable energy and property developers. Pipelines, contacts, and site data are managed directly on an interactive map — making spatial context central to the sales workflow, not an afterthought.


Personal Website · Open Source
sutan.co.uk
This website. Built in TypeScript with Vite and Tailwind CSS, deployed via CI/CD to GitHub Pages. Designed and directed from scratch using Claude Code — a working proof of the method described on this page.

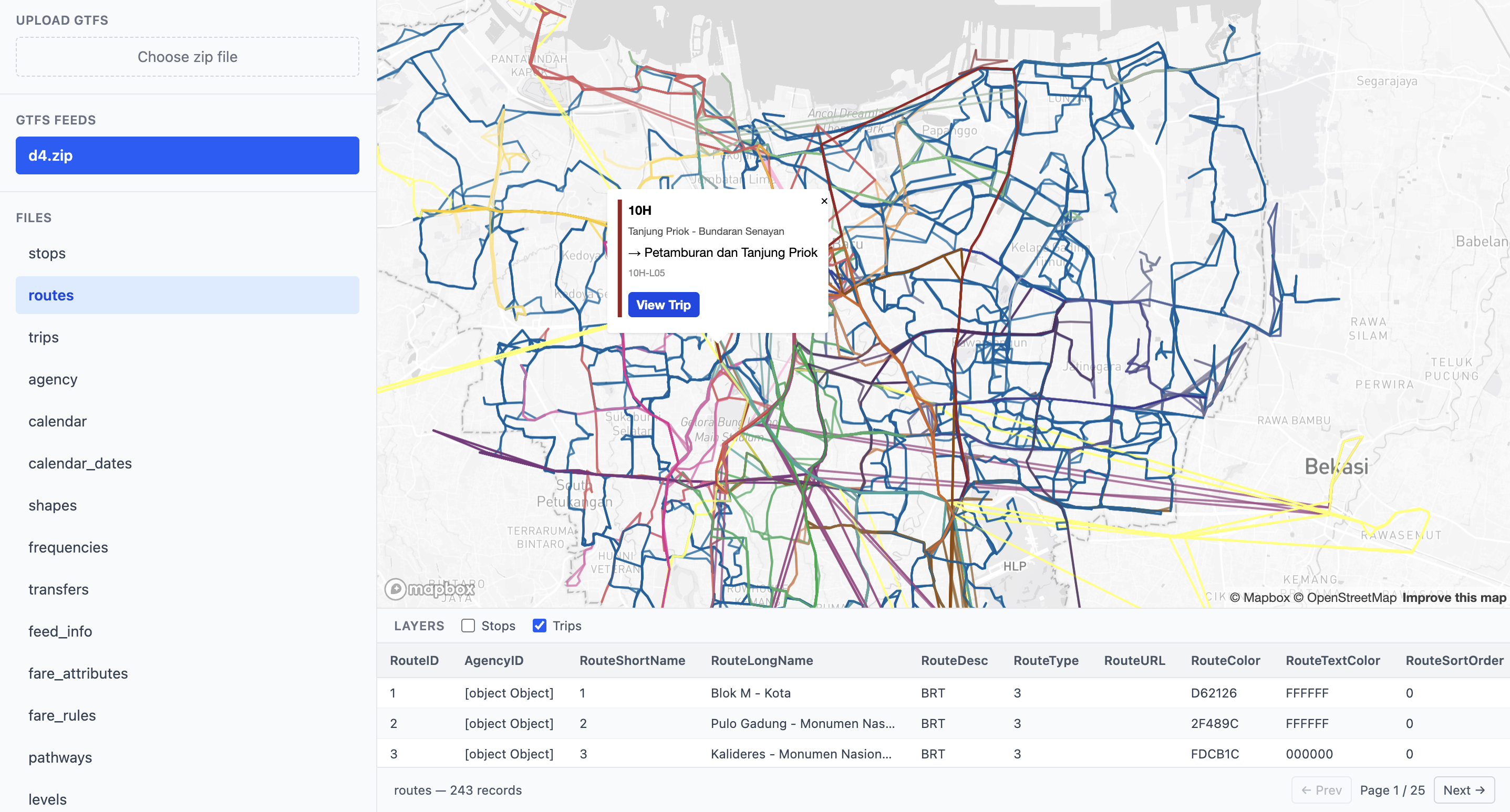
Open Source · Go · Transit
gtfs-viewer
An open-source Go library and tool to explore GTFS public transit models on a map. Designed to be intuitive for planners and engineers alike — clean API, zero unnecessary dependencies, published on pkg.go.dev.
